⚡ Quick Answer
Security bounties with Claude Code can work if you use it for recon, hypothesis generation, code review, and report drafting instead of blind automation. The money comes from a repeatable workflow that filters noise fast, validates findings manually, and writes cleaner submissions than most hunters do.
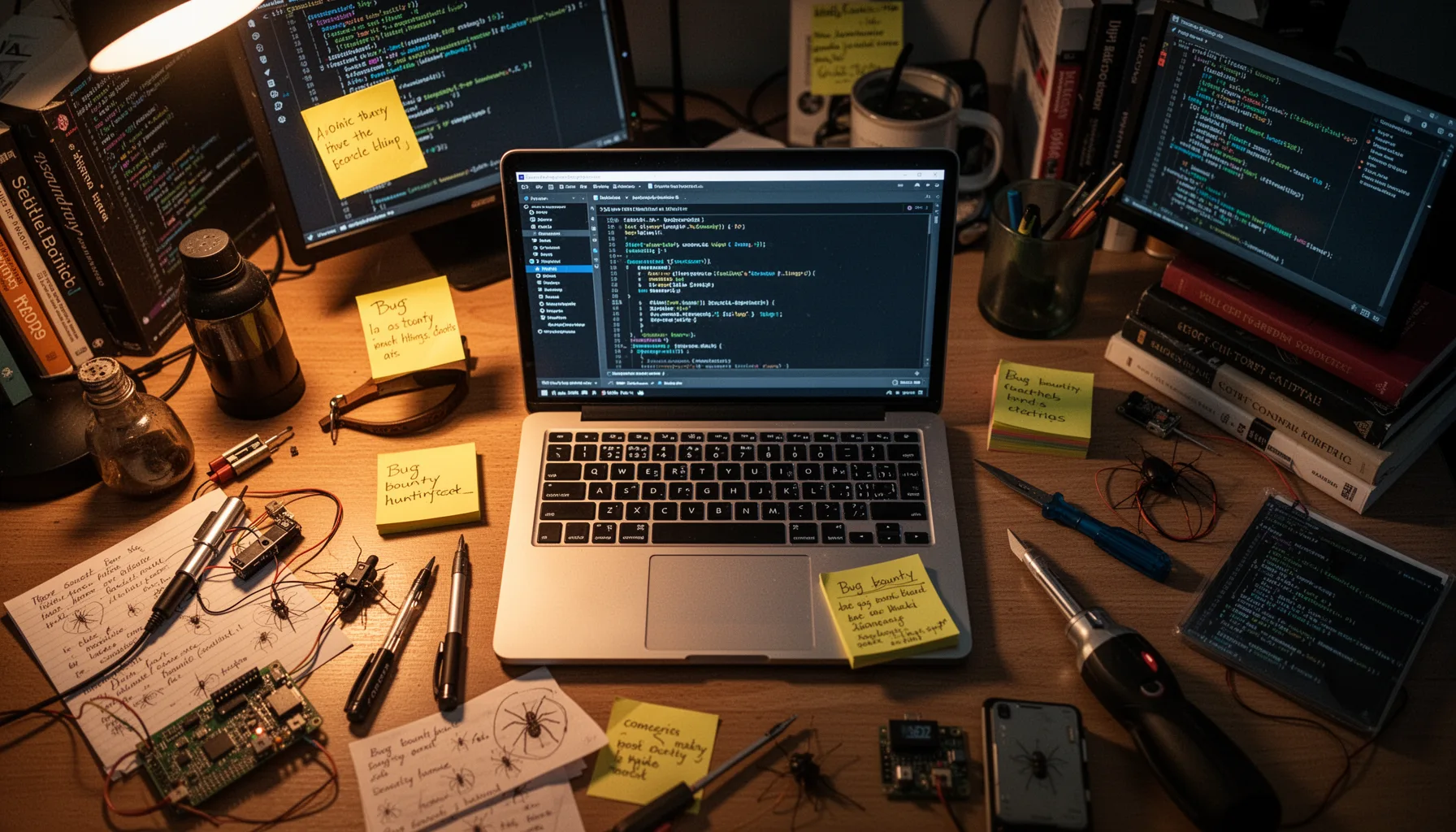
Security bounties with Claude Code sound flashy, sure, but the money usually comes from boring discipline. That's the hook. Most bounty hunters don't miss because they lack clever ideas; they miss because they get buried in low-signal recon and turn in reports that don't land. We've watched the same pattern play out across HackerOne and Bugcrowd: the people who earn consistently build systems, not vibes. Worth noting.
Why security bounties with Claude Code work better than manual-only hunting
Security bounties with Claude Code pay off because the tool compresses repetitive thinking, not because it mysteriously uncovers zero-days. That's the distinction that counts. When I size up a fresh program, I rely on Claude Code to cluster subdomains, summarize JavaScript endpoints, sketch likely attack surfaces, and point to places where auth logic probably needs human scrutiny. In practice, that trims first-pass recon by hours on medium-sized scopes. Fast matters. HackerOne said in its 2024 Hacker Powered Security Report that valid reports now come more often from a smaller pool of highly active researchers, which suggests throughput matters nearly as much as raw talent. That's a bigger shift than it sounds. If you're still reading every JS bundle and every OpenAPI spec by hand, you're picking slow over paid. Simple enough. A concrete example comes from Shopify-style asset sprawl, where Claude Code can ingest route files and client-side calls, then surface forgotten admin paths that deserve manual authorization testing.
What is my Claude Code bug bounty workflow from scope to submission
My Claude Code bug bounty workflow starts with scoped asset collection, then moves into prioritization, validation, and report drafting in that exact order. But the order matters more than any single prompt. First, I feed in-scope domains, program policy, known exclusions, and prior disclosure patterns into Claude Code so it can suggest a ranked recon plan instead of another generic checklist. Then I use it to parse nuclei output, JS endpoint lists, Wayback data, and GitHub exposure clues so I can ditch duplicate junk fast. Here's the thing. After that, I manually test only the highest-signal paths: broken access control, insecure direct object references, exposed debug features, S3 or GCS misconfigurations, and weak workflow assumptions. That's where payouts live. On one fintech target, Claude Code helped me connect an internal-looking GraphQL mutation to a user role mismatch; manual verification turned that into a valid privilege escalation report worth $1,500. And once the bug is confirmed, I use Claude Code to draft a tight reproduction path, impact statement, CVSS rationale, and remediation notes before I rewrite every line myself. We'd argue that's the sane split.
How to use AI for bug bounty hunting without flooding yourself with false positives
How to use AI for bug bounty hunting well comes down to one rule: never let the model decide a finding is real. That sounds obvious, yet plenty of hunters still do it. Claude Code is strongest when you ask it to explain suspicious behavior, compare intended versus observed access controls, and suggest negative test cases from app logic. It's much weaker when you dump scanner output and ask, 'Which of these are vulnerabilities?' because that prompt invites hallucinated certainty. Bad trade. Google's Project Zero and Trail of Bits have both stressed, in different contexts, that security work depends on precise validation and reproducibility rather than plausible-sounding analysis, and AI doesn't change that bar. Not quite. So I make Claude Code produce test hypotheses, not verdicts, and I require two manual confirmations before I write a report. A simple example: on a private program, Claude Code flagged a password reset flow as likely weak because the token length looked short in front-end code, but manual testing showed the real server-side token was longer and rate-limited, which saved me from a useless submission. Worth noting.
What real bug bounty payouts with Claude Code actually look like
Real bug bounty payouts with Claude Code usually look modest at first, then they compound, because consistency beats one lucky critical. That's not sexy, but it's true. My own pattern with AI-assisted security bounty hunting has been more $250 to $2,000 wins than dramatic five-figure headlines, and those smaller hits add up when the workflow stays disciplined. Bugcrowd's 2024 Inside the Mind of a Hacker report found that bounty hunters increasingly favor efficient tooling and repeatable specialization, which lines up with what many of us see in the field. Specialize or stall. The best Claude Code use cases for payout tend to be auth flaws, exposed admin functions, sensitive data exposure, and business logic breaks where the model can summarize lots of code fast and suggest edge cases a tired human might miss. One clean example came from a SaaS target where Claude Code summarized tenant isolation assumptions across route handlers, helping surface an IDOR chain that paid $900 after manual proof. We'd argue the real value isn't that Claude Code found the bug by itself; it got me to the right hypothesis before fatigue won. That's a bigger shift than it sounds.
Which best AI tools for bug bounty hunters pair well with Claude Code
The best AI tools for bug bounty hunters usually complement Claude Code instead of replacing it, with each tool covering a different part of the workflow. Claude Code shines at codebase reasoning and iterative analysis inside a developer-style loop, while Burp Suite Professional handles interception, replay, and extension-driven testing with much more precision. And Amass, httpx, subfinder, katana, ffuf, nuclei, and jq still do the heavy lifting for enumeration and filtering because deterministic tools beat language models on raw collection every single time. That's why my stack stays mixed. For browser-side inspection, I often pair Claude Code with Burp's Logger++, Param Miner, and Autorize, then use AI to interpret the patterns that show up instead of asking it to generate noise. Simple enough. GitHub Copilot and Cursor can help during proof-of-concept scripting, but Claude Code feels stronger when I need longer-form reasoning over routes, handlers, middleware, and report structure. A practical setup on a modern Next.js target might use katana for crawling, Burp for live testing, and Claude Code for explaining auth middleware gaps across API and page routes. Worth noting.
Step-by-Step Guide
- 1
Define the scope first
Start by pasting the exact program scope, exclusions, and safe-harbor rules into Claude Code. Then ask it to summarize what is fair game and what would create compliance risk. This sounds basic, but it prevents wasted recon on out-of-scope assets and cuts the odds of writing reckless prompts.
- 2
Collect assets systematically
Gather subdomains, historical URLs, JavaScript files, public repos, and technology fingerprints with your usual recon stack. Then feed those artifacts into Claude Code in batches and ask for endpoint clustering, auth-sensitive surfaces, and weird legacy patterns. You'll get more value from structured inputs than from one giant dump.
- 3
Generate test hypotheses
Ask Claude Code to produce ranked hypotheses for access control, workflow abuse, secrets exposure, and state transition issues. Force it to explain why each hypothesis might be valid and what evidence would disprove it. That framing keeps the model analytical instead of theatrical.
- 4
Validate findings manually
Reproduce every candidate issue by hand in Burp Suite, the browser, or a purpose-built script. Confirm that the behavior is actually exploitable, within scope, and not blocked by intended controls. If you can't prove impact yourself, don't submit it.
- 5
Draft cleaner reports
Use Claude Code to turn your notes into a submission with reproduction steps, expected versus actual behavior, business impact, and remediation ideas. Then rewrite key lines so the report sounds like your own tested conclusion rather than a model's polished guess. Triagers reward clarity more often than flair.
- 6
Track payout patterns
Log every submission, including target type, bug class, severity, duplicate status, and payout amount. Then ask Claude Code to spot which bug classes and program types produce the best return on your hours. That's how an occasional win becomes a repeatable system.
Key Statistics
Frequently Asked Questions
Key Takeaways
- ✓Claude Code works best as a force multiplier, not a replacement for human testing.
- ✓The highest ROI usually comes from recon triage, code review, and report writing.
- ✓Real payouts usually come from boring bugs found consistently, not flashy one-off chains.
- ✓Good prompts matter, but scoped targets and validation matter far more.
- ✓If your workflow can't cut false positives, AI will waste your time.