⚡ Quick Answer
The LiteLLM attack vulnerability exposed a deeper issue than one compromised package: many AI apps built fast with copied code and unchecked dependencies share the same weak points. If your tooling can auto-install packages, trust MCP plugins blindly, or access local secrets without isolation, your setup probably carries similar supply-chain risk.
People are searching for the LiteLLM attack vulnerability, but the package compromise points to something meaner underneath. A lot of vibe-coded apps make easy prey. Reports yesterday tied litellm v1.82.8 to a three-stage backdoor that could harvest SSH keys, cloud credentials, Kubernetes configs, and crypto wallets from machines that installed it. And the discovery reportedly happened inside Cursor through an MCP plugin path. That isn't some stray coding slip. It's a warning flare for the wider AI infrastructure stack covered in the pillar on AI Infrastructure, Deployment, and Platform Decisions.
What happened in the LiteLLM attack vulnerability incident?
The LiteLLM attack vulnerability incident centered on a malicious package release, reportedly litellm v1.82.8 on PyPI, with a staged backdoor built to pull sensitive files and credentials off developer machines. That's the plain answer. Reported targets included SSH keys, cloud credentials, Kubernetes configuration files, and crypto wallets. So the attack appears aimed at both infrastructure access and straight financial theft. LiteLLM's scale makes this not trivial. The package has been linked to roughly 97 million downloads per month, which gives any compromise an ugly blast radius. According to Sonatype's 2024 State of the Software Supply Chain report, open source malware packages rose 156% year over year. This case lines up with that trend. And the discovery reportedly surfaced inside Cursor when an MCP plugin path exposed the compromised dependency. We'd argue that's a bigger shift than it sounds. When an AI developer toolchain can ingest code this dangerous, the issue isn't just PyPI moderation. It's developer trust habits too.
Why vibe coded app security vulnerabilities look a lot like this
Vibe coded app security vulnerabilities usually begin with speed-first shipping, copied snippets, and dependency chains nobody really inspects end to end. That's the uncomfortable part. Teams building AI wrappers, internal copilots, and hackathon-grade tools often chase delivery over isolation, especially when the product supposedly just calls models and reads files. Not quite. Those apps usually sit on laptops or servers packed with credentials, local repos, tokens, and customer data. So the attack surface runs wider than many founders think. GitHub's 2024 developer surveys and ecosystem reports have repeatedly pointed to developers leaning harder on AI-assisted coding. And that speeds up package adoption without tightening review discipline. A concrete example sits in the rise of Cursor, Replit, and VS Code extensions. Plugins there can touch broad local context. Here's the thing. We'd argue vibe-coded isn't an insult in this case. It's a description of software produced at high velocity with very little operational drag, and that's exactly why attackers reach for it. Worth noting.
How a malicious PyPI package AI tools trust can steal SSH keys and cloud credentials
A malicious PyPI package AI tools trust can steal SSH keys and cloud credentials because installation often gives code immediate execution on machines that already store privileged files. Here's the core issue. Developers often assume package install means package safety, but Python packaging doesn't promise that. Since typosquatting, maintainer compromise, and release pipeline abuse all happen, that assumption falls apart fast. Once malicious code runs, it can enumerate directories, read kubeconfig files, scan for AWS credentials, and exfiltrate browser or wallet data if the environment allows it. According to Veracode's 2024 State of Software Security, 70% of organizations carry security debt in open source libraries. That suggests many teams already struggle to patch known issues. Never mind hidden backdoors. In AI tooling, the risk expands because agents and plugins often automate installs, environment setup, and repository access. That convenience turns into liability quickly. We think too many teams still treat package managers like app stores. They should treat them as raw code execution channels. Simple enough.
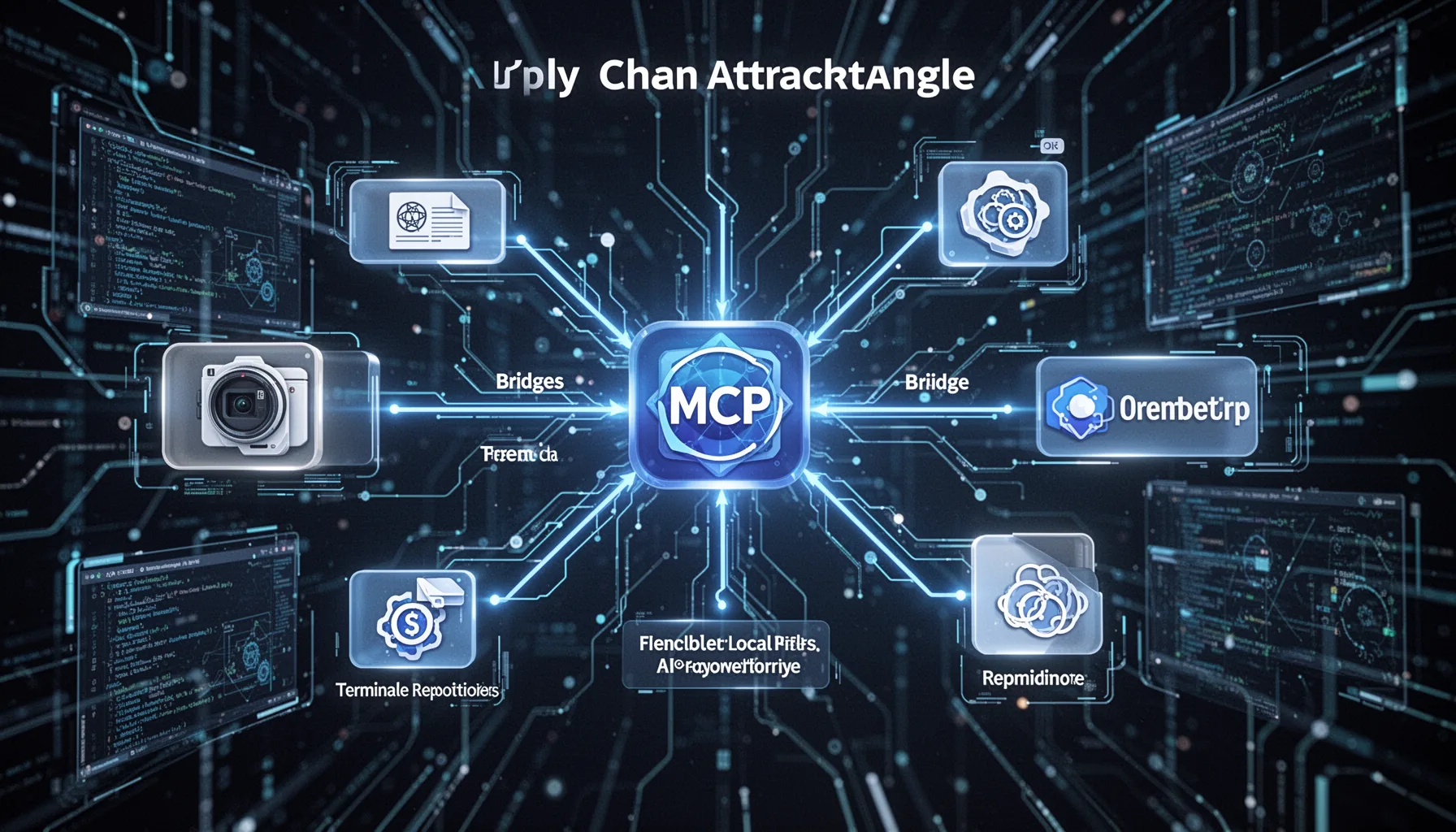
What the MCP plugin supply chain attack angle means for AI developer tools
The MCP plugin supply chain attack angle matters because AI developer tools now rely on tool bridges that can reach local files, terminals, repositories, and cloud-connected workflows. That's where things get real. MCP itself isn't the villain. It's a protocol pattern for connecting models to tools. But if a plugin chain includes compromised packages, weak signing practices, or broad local permissions, the whole stack becomes a soft entry point. The U.S. Cybersecurity and Infrastructure Security Agency has spent years warning about software supply chain compromise through dependency abuse and weak verification. AI toolchains now inherit that old mess in a new wrapper. Cursor is the named example here, but the lesson travels just as well to custom internal copilots and agent runners built on LangChain, LlamaIndex, or homegrown wrappers. And our take is blunt: AI infrastructure teams should stop treating plugin ecosystems like harmless productivity glue. They're part of the attack surface. Full stop. That's worth watching.
Step-by-Step Guide
- 1
Freeze suspicious dependencies immediately
Pin versions and stop automated upgrades the moment a supply-chain issue surfaces. Pull fresh hashes for critical packages and compare them to approved records. Speed matters here, because every unattended install widens exposure.
- 2
Audit package provenance
Check maintainer history, release timing, hashes, and repository links before trusting updates. Use tools that validate signatures or provenance attestations where available. If a package appears suddenly altered, assume compromise until proven otherwise.
- 3
Isolate developer secrets
Move SSH keys, cloud credentials, and wallet access out of default local paths where possible. Use short-lived tokens, hardware-backed auth, and role-based access controls. A stolen laptop secret should not unlock production.
- 4
Sandbox AI developer tools
Run copilots, package installs, and plugin workflows in contained environments. Containers, VMs, or remote dev boxes reduce what malicious code can reach. Convenience drops a little, but the blast radius drops a lot.
- 5
Review MCP and plugin permissions
Inventory every plugin, tool connector, and local access grant in your AI stack. Remove anything that can read files, execute shell commands, or install dependencies without a strong reason. Most teams have more access turned on than they realize.
- 6
Create a rollback and rotation plan
Prepare scripts and runbooks for key rotation, token revocation, and environment rebuilds. If compromise happens, response time decides how expensive the mess becomes. Security plans that live only in Notion won’t save you at 2 a.m.
Key Statistics
Frequently Asked Questions
Key Takeaways
- ✓The LiteLLM incident wasn't isolated; it pointed to common weak spots across AI toolchains.
- ✓Vibe-coded app security vulnerabilities often begin with dependency trust and little to no review.
- ✓A malicious PyPI package can hit local secrets, cloud tokens, and wallets fast.
- ✓MCP plugin supply chain attack risk climbs when tools run with broad local access.
- ✓Teams need package signing, sandboxing, and secret isolation for AI developer tools.